Datasheet

Own the Future: The New Standard in SAP S/4HANA Upgrades
Trusted by 3,000+ brands:
Whether you’re driving business innovation or getting on S/4HANA migration journey, Panaya ensures you’re well-informed before making any system modifications. With Panaya, you can pinpoint impact, minimizing risks, reduce code correction efforts, automate end-to-end test cycles, and navigate changes with full visibility and control. From initial planning to go-live, Panaya guides you safely through every step.
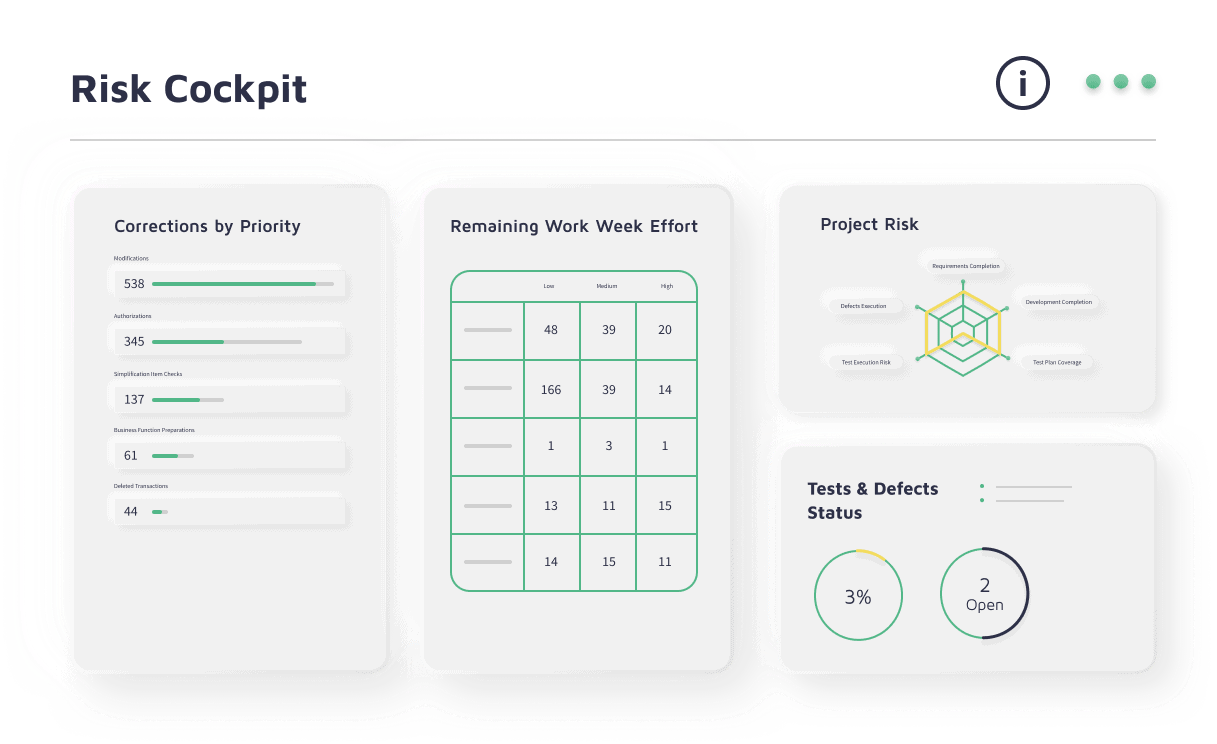
Navigate confidently to risk-free go-live by visualizing the impact of any SAP change in advance.
Accelerate testing processes and save on resources with No-Code test automation.
Proactively control your project and team progress with real-time insight into each step.

Gain complete coverage, visibility, and control throughout all stages of the SAP S/4HANA migration journey. Accelerate efficiency and innovation while minimizing risk and business disruption.
Orchestrate and streamline SAP end-to-end testing processes, with one platform uniting Test Management, Codeless Test Automation, and Change Impact Analysis.
Accelerate testing processes, optimize resources and embrace change and innovation with a user-friendly SaaS solution.
Reduce the time, cost and risk of SAP Changes with one platform for change impact analysis, transport remediation and collaborative testing.
Gain real-time insights to ensure you deliver SAP changes quickly and safely.
Easily navigate through every step of ECC, EHP, and SPS upgrades.
Reduce costs and effort by half while eliminating business risk – automatically planning, scoping, prioritizing, and testing all your ECC changes to guarantee risk-free go-live.



Datasheet

Own the Future: The New Standard in SAP S/4HANA Upgrades
White Paper
How to Make SAP Testing Work For You
Datasheet

Welcome To The Future of ERP & Business Application Testing
Datasheet
Accelerate SAP Upgrades & Migrations with Automatic Code Corrections
Panaya uses AI-powered change intelligence and impact analysis to analyze your SAP system and instantly determine the impact of any change—whether it’s a transport, code update, or configuration change. It automatically highlights impacted objects, suggests corrections, and optimizes test plans using AI / machine learning algorithms supplemented by 2 decades of SAP domain expertise. This enables faster delivery, reduced manual effort, and risk-free SAP projects—from change to testing and finally deployment.
Panaya supports a wide range of SAP projects, including SAP S/4HANA migrations (Brownfield, Greenfield and Bluefield/SDT implementations) incl. RISE and GROW, ECC and EHP upgrades, support package updates and test automation projects. Whether you're undergoing a major transformation or making routine changes, Panaya’s platform delivers automated impact analysis and end-to-end SAP testing to help manage any project effectively and efficiently.
SAP system changes—no matter how small—can carry big risks. Panaya helps you navigate SAP modifications confidently by identifying which code, transactions, or business processes will be impacted before you make the change. It offers guided remediation suggestions and creates targeted test plans, ensuring a smooth implementation without unexpected disruptions.
Panaya reduces risk by delivering real-time impact analysis for every SAP change—be it technical or functional. It identifies areas at risk, suggests remediation actions, and eliminates unnecessary testing through risk-based test planning. With Panaya, customers reduce defects, rework, and go-live failures, ensuring stable and predictable SAP project delivery.
Yes. Panaya offers full project visibility through real-time dashboards, heatmaps, and reports that track test execution, defect status, and milestone completion. This transparency empowers project managers, IT, and business stakeholders to stay aligned, identify bottlenecks early, and keep SAP projects on schedule.
Absolutely. Panaya accelerates SAP ECC and EHP upgrades by performing automated impact analysis and generating targeted test plans. It identifies required code adaptations, suggests fixes, and automates test cycles—cutting project effort 50% and more. Whether it’s a full upgrade or a support pack implementation, Panaya ensures a faster, safer upgrade with zero disruption to business processes.
Panaya complements RISE with SAP by adding critical capabilities like automated impact analysis, test management, and AI-powered test automation. While RISE provides the cloud infrastructure and business process tools, Panaya ensures that every change is validated before go-live. It helps SAP customers and system integrators accelerate timelines, minimize risk, and protect business continuity during their cloud transformation.
Unlike traditional testing, ALM tools and spreadsheets, Panaya combines impact analysis, test management, and no-code automation into a single platform built specifically for SAP. It doesn’t just help you test—it tells you exactly what to test and automates the rest. This unique business-centric approach helps enterprises reduce test scope, avoid post-go-live issues, and align business and IT teams around quality.
Panaya is designed to bring IT and business teams together. Technical users benefit from code-level analysis and automated fixes, and most of all—the support of their business counterparts. Business users can participate in UAT with easy-to-use, browser-based testing workflows—no training or coding required. Everyone works on the same platform, with real-time visibility into project status.